US Senate Amendments Target DeFi Developer Liability and Protocol Autonomy
A slate of proposed amendments to the CLARITY Act would make writing open-source financial software a regulated, and potentially criminal, activity in the United States. Filed by a group of Democratic senators including Elizabeth Warren, the changes aim to dismantle the legal distinction between bui

A slate of proposed amendments to the CLARITY Act would make writing open-source financial software a regulated, and potentially criminal, activity in the United States. Filed by a group of Democratic senators including Elizabeth Warren, the changes aim to dismantle the legal distinction between building a decentralized protocol and operating a bank. They would assign financial intermediary liability to developers, give federal agencies the power to sanction autonomous code, and create new criminal penalties for authors whose software is used for illicit ends.
The proposals are a three-pronged attack on the architecture of decentralized finance.
First, they go after the idea that you are only a money transmitter if you actually transmit the money. A section of the underlying bill, the Blockchain Regulatory Certainty Act, was meant to create a safe harbor for developers who don’t take custody of user funds. Several amendments would gut this protection, with one deleting it entirely. The rewrite would expose non-custodial software developers to the full weight of the Bank Secrecy Act. The regulatory burden would shift from the party controlling the assets to the party who wrote the code. The original bill drew a line between writing software and holding cash. These amendments are designed to erase it.
Second, the changes invent a new standard for developer liability. A developer could be found criminally liable for creating code that "facilitates" financial crime, even if they had no knowledge of the specific act. The proposed standard is "reckless disregard," which is a prosecutor's dream. They would only need to argue that a developer should have known their general-purpose tool might one day be used by a criminal. This makes the author of an open-source protocol responsible for all future uses of it by anyone, anywhere. It makes every developer a potential accomplice to a crime they didn't know was happening.
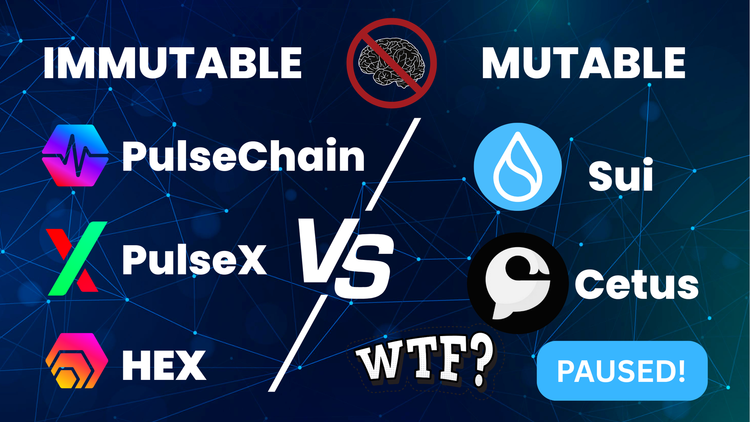
Third, the amendments provide a legislative workaround to a recent court defeat. After the Treasury sanctioned the Tornado Cash protocol, a federal court ruled that an autonomous, ownerless smart contract is not "property" and cannot be sanctioned. An amendment from Senator Reed explicitly authorizes the Treasury to sanction smart contracts anyway, regardless of whether they have an owner. The court said the Office of Foreign Assets Control overstepped its authority. This amendment gives the agency a legislative hall pass to do it again, creating a kill switch for code the government dislikes.
None of this is happening in a vacuum. It is the next logical step in a campaign that began with the Treasury's sanctioning of Tornado Cash. When that action was challenged and its legal basis questioned in court, the state's response was not to reconsider its strategy, but to rewrite the law. The amendments are an attempt to legislate the outcome the courts were hesitant to grant.
The core strategy is to treat decentralization as a legal fiction. Regulators see creators and maintainers, so they are trying to map the legal duties of a bank onto them. In their view, a validator is a teller and a core developer is a compliance officer, even if neither has any ability to stop or reverse a transaction. This is the same logic used during the 1990s crypto wars, when the government tried to classify encryption software as a munition to control its spread. That effort failed. This is round two, with finance as the battlefield.
If these amendments become law, the risk of building open-source financial tools in the US will become untenable. Venture funds and foundations will back away. Development will flee to other jurisdictions or go underground. The precedent of sanctioning autonomous code is a particularly potent one, giving the state a mechanism to target any system designed to operate without a central point of control.
The choice this forces on a developer is stark. Build your protocol with backdoors for surveillance and control, or risk being treated as a criminal enterprise. The fight is no longer about the regulated exchanges at the network's edge. The state is attempting to write itself into the architecture of systems designed to operate without a master, and it is using the threat of prison to hold the pen.
---
Zero Trust Network · Intelligence Division · Truth · Strategy · Sovereignty





Discussion