ZetaChain exploit reveals the failure of human gatekeeping in bug bounties
ZetaChain recently suffered a $334,000 exploit targeting its cross-chain gateway contract, an incident that was entirely preventable. The vulnerability used to drain funds across Ethereum, Arbitrum, Base, and BSC had been previously flagged by a researcher through the project’s bug bounty program. H
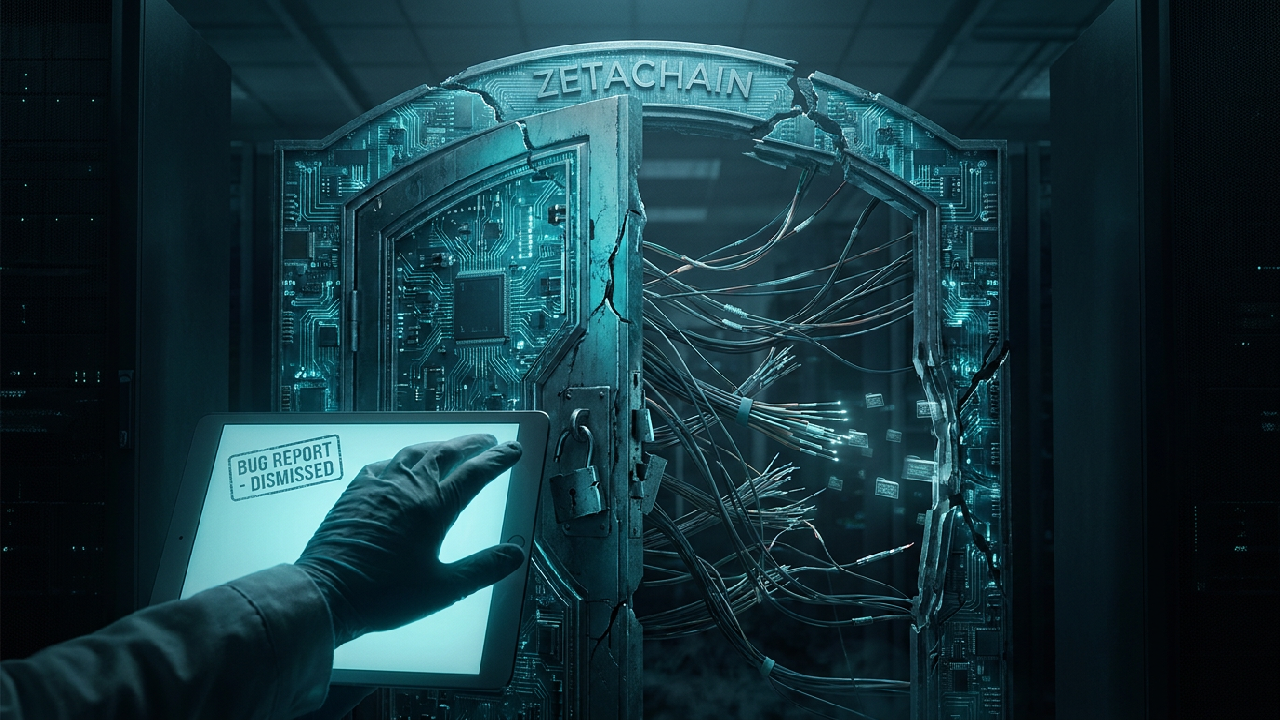
ZetaChain recently suffered a $334,000 exploit targeting its cross-chain gateway contract, an incident that was entirely preventable. The vulnerability used to drain funds across Ethereum, Arbitrum, Base, and BSC had been previously flagged by a researcher through the project’s bug bounty program. However, the core team dismissed the report, categorising the flaw as intended behaviour rather than a critical risk. The attacker subsequently utilised the exact vector described in the report to execute nine transactions from wallets controlled by the protocol.
The failure here is not merely technical, but architectural and procedural. The exploit relied on a combination of three design flaws that exposed the inherent dangers of centralised trust in smart contract execution. First, the gateway permitted arbitrary cross-chain instructions from any user without restriction. Second, the execution environment lacked a robust blocklist, failing to prevent basic token transfer functions from being called maliciously. Third, the protocol relied on unlimited spending permissions from wallets that had previously interacted with the gateway, a common but dangerous shortcut in DeFi development.
When a protocol team acts as the sole arbiter of what constitutes a bug, they create a single point of failure in the security lifecycle. By dismissing the researcher’s report, the ZetaChain developers prioritised their own internal assumptions over external verification. This human gatekeeping allowed a known vulnerability to remain live, proving that even a well-funded bug bounty program is useless if the trust model remains closed and opaque. The attacker, who funded their wallet via Tornado Cash and deployed a bespoke drainer contract, simply followed the logic the developers claimed was working as intended.
In a Zero Trust environment, security cannot depend on the discretion of a core team or their willingness to admit a mistake. True sovereignty requires that the code itself enforces restrictions, rather than relying on developers to manually validate threats. This incident confirms that as long as protocols maintain arbitrary call functionality and unlimited approvals, they remain custodial by proxy, holding the keys to user and protocol funds until a third party decides to turn them.
---
Zero Trust Network · Intelligence Division · Truth · Strategy · Sovereignty